By: David Gracey
Over the past several years, there have been several high-profile security breaches in the news. Cyber security is a big business and growing. And for good reason: there are thousands of attempts every day on private businesses and government computers. Although the big hacks represent a very few breaches, they are the most public for a variety of reasons.
Several news organizations and the U.S. government have pieced together compelling arguments for the sources of many of these hacks being Russia, China and North Korea; all three having different motivations for their alleged attacks. David Sanger, chief Washington correspondent for the New York Times, has reported extensively on these state-sponsored cyber crimes. His recent book, The Perfect Weapon, details many of the topics included in this Tuesday Tip.
Sony: Although North Korea has very limited Internet inside their country, they have developed an army of specialists trained in hacking into other computer systems. They station their best and brightest hackers outside of North Korea in countries like the Philippines, Vietnam and Japan. Most of these hackers are young males and prefer to be near a beach (who wouldn’t?) so the allure is high. In 2014, when Sony’s subsidiary, Columbia Pictures, was about to release the comedy The Interview, starring Seth Rogen, which poked fun at North Korea’s leader, Kim Jong-un, their government went ballistic. They threatened Sony and the United States with apocalyptic violence if the movie was released. (North Korea doesn’t really understand satire but the movie probably would have been a much bigger flop had they not made such a big deal out of this). Sony wanted to cancel the launch but was persuaded by the Obama administration to proceed. They cancelled most of their preview parties and decided to release the movie in digital form and limited theater release. The North Korean government put their army into action, which already had their hacking tentacles well into Sony’s computer systems, wiped out hard drives of thousands of computers, released reams of internal emails which ended a few careers and stole digital copies of upcoming movie releases and shared them in full on the Internet. They did little to hide their tracks as part of their point was retaliation.
Seth Rogen and James Franco, The Interview (2014)
Ukraine and The DNC: The leadup to the 2016 presidential election was highly charged. Donald Trump was stirring up his base with allegations of “fake news” and “rigged elections” while Hilary Clinton was trying to stave off a charge from her left by Senator Bernie Sanders. Russia, with Vladimir Putin’s full knowledge and approval (he would deny this), had been trying out several different tactics with cyber warfare. Their most successful had been infiltrating Ukraine’s power grid and the computers that ran them. On the eve of an invasion by Russian troops, the Russian hackers (again, embedded in the military) had launched their attack by activating the infected Ukrainian computers to shut down the power grid. Ukraine lost power for hours while the military began its aggression. They also took over several key websites used by the Ukrainian government to post updates and communicate with its people. Putin’s use of hackers for political gains were new and the United States government didn’t know how to respond to the Ukrainian hack.
When the 2016 U.S. election rolled around, Russia tried something new: they used social media, primarily Facebook, to disrupt our election process. The hackers created groups on Facebook, choosing one political side or the other, and created confusion and stoked the bases of both parties by spreading news that was indeed fake. But their most damaging achievement was a complete infiltration of the Democratic National Committee and the people who worked there. Putin was able to access tens of thousands of emails, obtain passwords and find out key information about the campaign, including the DNC’s private work in favoring Clinton over Sanders. His goal was to undermine our democratic process and in many ways he was successful.

The Ukrainian power grid fell victim to a Russian cyber attack in December of 2015.
OPM: The People’s Republic of China is into hacking for the economic benefit. They see little difference in their economy and national security, so they treat them equally. Their state-sponsored hacks, run by a unit of the military called PLA Unit 61398 have targeted companies from around the world, including and especially, those based in the United States. But their most public and well-known hack came in 2015 when they accessed most of the Office of Personnel Management (OPM) of the United States government. They were able to access millions of individual’s Social Security numbers and medical records. There were also able to see who applied for what job (including spying) in the U.S. government, background checks, prior criminal activity and just about anything else. This was a treasure trove of information for the PRC and they were looking to use this information for the PRC’s leadership, not merely to sell the information on the black market. The U.S. and a few private cyber security companies were able to track the hack back to China. We were able to hack into the Unit 61398 command center, enabled the cameras on the workers’ laptops, watched them while they hacked our computers and monitored their keystrokes. The hack of the OPM is one of the most damaging hacks in U.S. history.
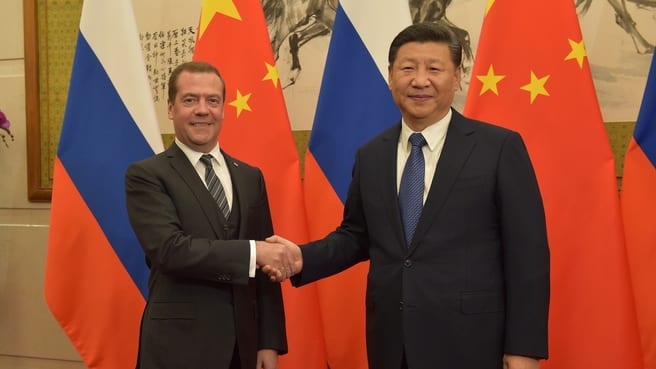
Prime Minister of Russia Dmitry Medvedev (left) & President of China Xi Jinping (right)
What Can I do to Protect Myself?
Small businesses and individual computer users are also vulnerable to attack. Just because you are not a billionaire or a publicly traded company doesn’t mean the bad guys won’t target you. It is tough to stay safe if you are targeted but if you can stay of most of their radars, that can go a long way. But it only takes one person to click on something to unleash a virus or malware.
1. Use complex passwords and use a unique password for each of your applications. A password manager like LastPass can help.
2. Don’t click on links or open attachments. If someone emails you asking for something that seems a bit odd, pick up the phone and call them. Otherwise, delete the email.
3. Keep your computer and anti-virus software up-to-date.