by Tony Rushin
773 million email addresses and passwords were widely distributed by the “bad guys” in January, 2019. The set – dubbed Collection #1 – came from over 2,000 hacked databases.
If you already have a password manager – we recommend LastPass – and use 2-factor authentication (2FA), skip to the bottom of this page for an advanced security check.
If you use – or have used – your email password as a password for any other applications (such as an online bank account or web app), you’ll want to change those passwords. Here is a link to a website where you can check to see if a password you have used has been compromised. Note: although this is a trusted site, I don’t recommend ever entering a current, valid password into any site on the internet. I suggest you enter an old, simple password that you previously used; that’s what I did and it came up with these results:

By the way, “pwned” is pronounced “owned”. A while back an online gamer thoroughly destroyed his opponent and mistyped “owned!” – it caught on in the gaming community.
Due to this massive breach, I suggest you take at least one of these actions immediately:
- Never, ever, EVER reuse a password. This practice is extremely risky – even if it’s a complex password. Once the bad guys get one of your passwords they immediately start trying it in your other accounts – and they use bots to do this so they can try it in thousands of places every minute. If you reuse a password, change them today!
- Start using a password manager today. The biggest reason people reuse passwords is because they don’t have an easy system for keeping them. LastPass is an easy-to-use online password manager that many of us at Network 1 use. Their free version will do everything you need to safely store your personal login credentials. You can set unique and incredibly complex passwords: LastPass stores them and – when you’re logged in to LastPass – logs in for you with a click of your mouse.
- Enable 2-factor authentication (2FA) wherever and whenever it’s available. Most bank portals have an option to turn-on 2FA. Once enabled, log in like you normally do and you will be prompted to enter the code that was sent to your mobile phone. This ensures that it is really you logging in and not a bad guy from Eastern Slaoustakia.
Simply take one of these steps today; you – and your bank accounts, credit cards and credit rating – will be glad you did.
Advanced Security Check
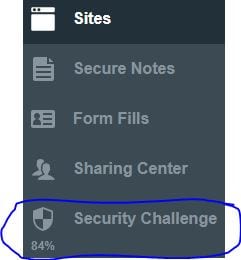
Here is the advanced security check I promised for those of you who already use a password manager. I can’t vouch for all password managers but I bet most have something similar to the Security Challenge LastPass has. Thanks to my colleague, Richard Stokes, who showed me this last week. When you click on the Security Challenge, LastPass analyzes all of your passwords looking for weak or reused passwords. It also attempts to identify any sites you store in LastPass to see if they have been recently compromised.
As you can see, I’ve got some work to do myself with a security score of 84%. The good news is that none of my passwords have been compromised. The other good news is that the LastPass Security Challenge found a few things that I would not have found on my own: 4 weak passwords plus a couple of sites where I was using a duplicate password. They provide me with all of the detail I need to quickly and easily make these changes… so you know what I’m doing as soon as I post this tip!