By David Gracey
 Recently we have noticed a trend with hackers demonstrating a new level of aggression and determination. The bad guys are getting cleverer — and more dangerous — in their methods of stealing our personal information. There are many different kinds of attacks and one of the most common is known as “phishing,” which is where the bad guys trick you into giving up your login and password for a particular service, like online banking or email. Once they have access to your account, they attempt to steal your identity, make fraudulent purchases or transfer funds from your bank accounts. This is scary stuff and it is important that you take, at a minimum, very simple and fundamental steps to protect yourself.
Recently we have noticed a trend with hackers demonstrating a new level of aggression and determination. The bad guys are getting cleverer — and more dangerous — in their methods of stealing our personal information. There are many different kinds of attacks and one of the most common is known as “phishing,” which is where the bad guys trick you into giving up your login and password for a particular service, like online banking or email. Once they have access to your account, they attempt to steal your identity, make fraudulent purchases or transfer funds from your bank accounts. This is scary stuff and it is important that you take, at a minimum, very simple and fundamental steps to protect yourself.
Here is a hack that occurred recently; this cautionary tale affected four of our clients who were all members of the same business group. To protect the innocent, we’ll call them Alice, Barney, Claire and Darrell.
Step 1: Alice is compromised. Alice gets an email of some sort asking her to reset her password, which she clicks on. This information is transmitted back to the bad guys but nothing happens to Alice’s computer so she doesn’t give the request a second thought. Unfortunately, Alice uses a single password for all of her online accounts, including her work email. The hacker then is able to access Alice’s email account and read all of her incoming and sent email without her knowledge. After doing some research by rooting around in her Sent Items and Calendar, the hacker figures out a few business groups Alice belongs to and targets specific individuals who Alice knows.
 Step 2: “Alice” sends emails. Once the hacker scumbag has identified some new targets, he logs into Alice’s email account (via webmail) during business hours and starts sending an email out to a small but targeted handful of people who know Alice. This includes Barney, Claire and Darrell. The email shows up as a “secure and encrypted” document. All three recipients have been well trained on IT security and are somewhat suspicious, but the email seems legitimate: Alice’s email is from her email server and has her full email signature along with it. Claire actually calls Alice to verify the email’s authenticity and the receptionist says Alice is in a meeting, so Claire sends Alice an email instead. The hacker is actively in Alice’s email account and replies to Claire stating yes, the email is legitimate and to “go ahead and open the secure document.” Claire then is prompted to enter her email address and password, thereby giving the bad guys even more information.
Step 2: “Alice” sends emails. Once the hacker scumbag has identified some new targets, he logs into Alice’s email account (via webmail) during business hours and starts sending an email out to a small but targeted handful of people who know Alice. This includes Barney, Claire and Darrell. The email shows up as a “secure and encrypted” document. All three recipients have been well trained on IT security and are somewhat suspicious, but the email seems legitimate: Alice’s email is from her email server and has her full email signature along with it. Claire actually calls Alice to verify the email’s authenticity and the receptionist says Alice is in a meeting, so Claire sends Alice an email instead. The hacker is actively in Alice’s email account and replies to Claire stating yes, the email is legitimate and to “go ahead and open the secure document.” Claire then is prompted to enter her email address and password, thereby giving the bad guys even more information.
Step 3: Claire calls Network 1 support. Claire is confused and suspicious so she calls the Network 1 Support Desk. This move saves her a LOT of hassle and (potentially) money. While Claire is fully describing what is going on to Network 1, Darrell calls the Support Desk and describes a similar email from Alice (after having entered his email address and password into the bad guy’s website) regarding a situation that is happening to him. The two Network 1 engineers overhear each other describing the issue and quickly realize Alice has been hacked. They immediately move to lock out Alice’s email account and assess the damage.
Step 4: Delivering bad news. Alice was still in her meeting but Network 1 got in touch with her by asking the receptionist to interrupt the meeting. Not knowing what was happening, Alice is told her email account has been hacked and is quick to point out “Oh, no! I use that password for everything.” Network 1 instructs Alice to immediately begin resetting passwords for all her other accounts: banking, office login, iPhone, Comcast, credit cards, etc. She does this manually but jumps right on it and avoids any fraudulent charges or further problems.
 Step 5: Damage control. The Support Desk is quickly able to determine the extent of the hack. With Alice’s email now locked, they identify all the emails that the hacker sent from Alice’s email account. It is limited to Barney, Claire and Darrell but probably would have been many more if timing had not worked in their favor. Fortunately, Barney and Darrell use a password management tool called LastPass so they are able to quickly change important passwords. Claire manually changes her passwords.
Step 5: Damage control. The Support Desk is quickly able to determine the extent of the hack. With Alice’s email now locked, they identify all the emails that the hacker sent from Alice’s email account. It is limited to Barney, Claire and Darrell but probably would have been many more if timing had not worked in their favor. Fortunately, Barney and Darrell use a password management tool called LastPass so they are able to quickly change important passwords. Claire manually changes her passwords.
Lessons and Reminders: here are a few easy steps to ensure that you stay hack-free:
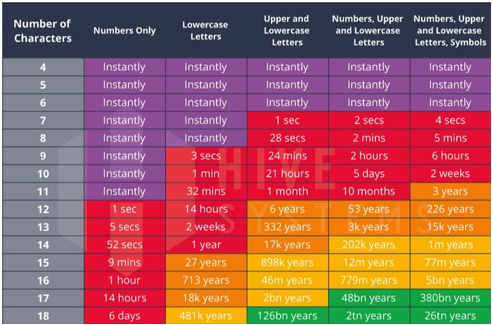
- Make passwords unique and hard to guess. Use a mix of uppercase, lowercase, numbers and special characters. Don’t use the same (or similar) passwords for various accounts. Use a password manager, as described in a previous Tip entitled Managing Strong Passwords, to create complex passwords and you’ll never forget a password, either. LastPass is free, easy to use and syncs over multiple devices.
- Trust but verify. Clicking on a link or attachment in an email transmits most viruses. If you aren’t expecting an email from someone, don’t click the link or attachment. If it looks important, call or email the sender to double check.
- Look for signs. Mouse over any link before you click on it and check the spelling of the website. Look for misspellings or grammatical errors in the link or in the email. Hackers that aren’t English-speakers often make these mistakes. Websites don’t need your login information. Never type them into a website unless you are SURE of where you are.
The bad guys are getting more effective at accessing our credit card, online banking and personal information. It is up to us to ensure we stay one step ahead of them.