In my 25+ year career I have worked with many different aspects of both the medical and information technology industries. My position with Network 1 perfectly melds those two acquired skill sets while also exposing me deeper into the back office side of proper data security and storage methodologies. I also manage many of our financial clients and I am quickly learning that there is very little difference between how each industry is regulated by big brother. Both the medical and financial industries work with sensitive personal information that, if compromised by the bad guys, could spell big doom for both the patient/client and the organization they have trusted with said sensitive personal information.
In my 25+ year career I have worked with many different aspects of both the medical and information technology industries. My position with Network 1 perfectly melds those two acquired skill sets while also exposing me deeper into the back office side of proper data security and storage methodologies. I also manage many of our financial clients and I am quickly learning that there is very little difference between how each industry is regulated by big brother. Both the medical and financial industries work with sensitive personal information that, if compromised by the bad guys, could spell big doom for both the patient/client and the organization they have trusted with said sensitive personal information.
 So, to make sure everyone follows the rules, bring in the governmental regulatory agencies. For the medical industry there are HIPAA and HHS, and the financial industry has FINRA and the SEC. Both industries have rulebooks that make sure everyone in that industry plays nice in the sandbox. For this article I will focus on the medical regulatory side, but don’t get too comfortable financial folks, you are also in the cross hairs…
So, to make sure everyone follows the rules, bring in the governmental regulatory agencies. For the medical industry there are HIPAA and HHS, and the financial industry has FINRA and the SEC. Both industries have rulebooks that make sure everyone in that industry plays nice in the sandbox. For this article I will focus on the medical regulatory side, but don’t get too comfortable financial folks, you are also in the cross hairs…
The Health Insurance Portability and Accountability Act (HIPAA) has been around since 1996 and has revolutionized the entire medical industry from top to bottom. Its main goal was to standardize and digitize all aspects of the medical industry so that patient information is both protected by, and freely flows through, the system with some form of uniformity. It basically makes sure that you can easily take your x-rays to another doctor for a second opinion and also that the doctors can quickly get paid for their services. This is great for the patients and providers alike, however, HIPAA circa 1996 did little to anticipate the proliferation of electronic Protected Health Information (ePHI) that we now see in the medical industry. Enter another congressional act in 2009, Health Information Technology for Economic and Clinical Health (HITECH).
 HITECH contains specific incentives designed to accelerate the adoption of Electronic Health Record (EHR) systems among providers and, as a side note, it also widens the scope of privacy and security protections available under HIPAA. This add-on to HIPAA increases the potential legal liability for non-compliance and provides for more “enforcement” (a governmental code word for fines). This is where many mega corporate hospital systems and single doc private practices have racked up millions and millions and millions of dollars in fines in just a few years.
HITECH contains specific incentives designed to accelerate the adoption of Electronic Health Record (EHR) systems among providers and, as a side note, it also widens the scope of privacy and security protections available under HIPAA. This add-on to HIPAA increases the potential legal liability for non-compliance and provides for more “enforcement” (a governmental code word for fines). This is where many mega corporate hospital systems and single doc private practices have racked up millions and millions and millions of dollars in fines in just a few years.
 This is such a “fun money maker” for the government that the HHS even has a “Wall of Shame” (https://ocrportal.hhs.gov/ocr/breach/breach_report.jsf ) dedicated to all offenders that have compromised 500 or more individual’s protected health information (PHI). As of this writing there are 1,381 scarlet letter practices on the wall starting on October 10th, 2009, when Brooke Army Medical Center (yea… a government institution…) lost “A binder containing the protected health information (PHI) of up to 1,272 individuals was stolen from a staff member’s vehicle. The PHI included names, telephone numbers, detailed treatment notes, and possibly social security numbers.” A quick Google search failed to show if there was any fine paid for this breach, just some “enhanced training and procedures”. The Office for Civil Rights (OCR), which is tasked with enforcing the law, is no longer so forgiving…
This is such a “fun money maker” for the government that the HHS even has a “Wall of Shame” (https://ocrportal.hhs.gov/ocr/breach/breach_report.jsf ) dedicated to all offenders that have compromised 500 or more individual’s protected health information (PHI). As of this writing there are 1,381 scarlet letter practices on the wall starting on October 10th, 2009, when Brooke Army Medical Center (yea… a government institution…) lost “A binder containing the protected health information (PHI) of up to 1,272 individuals was stolen from a staff member’s vehicle. The PHI included names, telephone numbers, detailed treatment notes, and possibly social security numbers.” A quick Google search failed to show if there was any fine paid for this breach, just some “enhanced training and procedures”. The Office for Civil Rights (OCR), which is tasked with enforcing the law, is no longer so forgiving…
 Two Hospitals in New York were a bit too lackadaisical with 6800 patients’ ePHI in 2010. Their lack of simple technical safeguards resulted in a server breach exposing “information including patient statuses, vital signs, medications and laboratory results, as well as 10 Social Security Numbers.” The 2014 fine handed down to New York-Presbyterian Hospital and Columbia University totaled $4.8 million… with an “M”… Million… (https://www.fiercehealthit.com/story/server-mishap-results-48-million-hipaa-settlement/2014-05-08 ). I doubt the bean counters at Presbyterian and Columbia had allowed for that “unexpected” expense in their budget for 2010. Has your practice allowed for it? Ask yourself this…
Two Hospitals in New York were a bit too lackadaisical with 6800 patients’ ePHI in 2010. Their lack of simple technical safeguards resulted in a server breach exposing “information including patient statuses, vital signs, medications and laboratory results, as well as 10 Social Security Numbers.” The 2014 fine handed down to New York-Presbyterian Hospital and Columbia University totaled $4.8 million… with an “M”… Million… (https://www.fiercehealthit.com/story/server-mishap-results-48-million-hipaa-settlement/2014-05-08 ). I doubt the bean counters at Presbyterian and Columbia had allowed for that “unexpected” expense in their budget for 2010. Has your practice allowed for it? Ask yourself this…
- Are all your laptops encrypted?
A $2 Million fine in 2014 for Concentra Health Services for 2 stolen laptops. https://www.fiercehealthit.com/story/ocr-levies-2-million-hipaa-fines-stolen-laptops/2014-04-23 ) - Are your servers secure online? Are you sure? Really Sure? Really REALLY Sure?
Utah Department of Health thought so too… in 2012 hackers stole over 780,000 individual’s information https://www.health.utah.gov/databreach/index.html. No fine yet… but it is coming… - Are your back up drives locked up tight? Can anyone walk into to your server closet right now because the door is unlocked? Go check… On April 18th, 2012 Emory Healthcare in Atlanta thought so, too… until they “misplaced” 10 small hard drives containing 315,000 individuals PHI. “Oops? My bad…” was not good enough.
https://www.eweek.com/c/a/Health-Care-IT/Emory-Healthcare-Data-Breach-in-Atlanta-Affects-315000-Patien ts-704506. Emory’s fine has yet to be levied but is sure to be in the many Millions… (Again, with an “M”…)
ts-704506. Emory’s fine has yet to be levied but is sure to be in the many Millions… (Again, with an “M”…)
So… what can you and your practice do about possible HIPAA compliance shortfalls?
 Simple: pay a few thousand for a certified compliance audit of your HIPAA and HITECH policies, then put a plan into place to fix what is broken. 2 years ago Network 1 hired a HIPAA compliance auditor to look under our carpets and in our closets for any possible compliance holes. They found some things we could do better and we immediately implemented those recommendations into our corporate culture. We have another audit in the works to see how we are doing.
Simple: pay a few thousand for a certified compliance audit of your HIPAA and HITECH policies, then put a plan into place to fix what is broken. 2 years ago Network 1 hired a HIPAA compliance auditor to look under our carpets and in our closets for any possible compliance holes. They found some things we could do better and we immediately implemented those recommendations into our corporate culture. We have another audit in the works to see how we are doing.
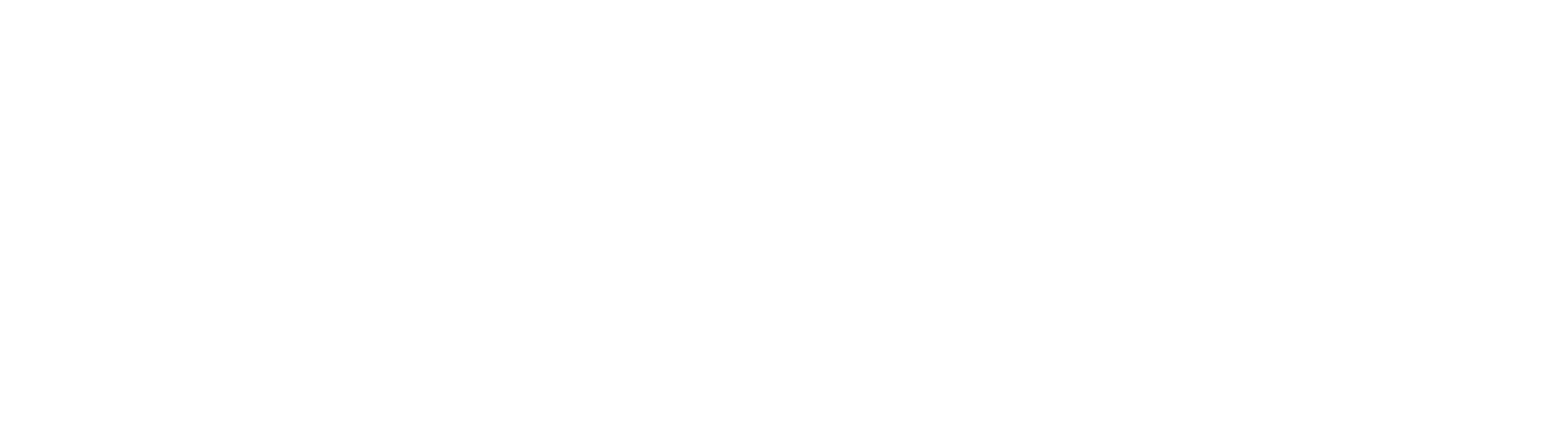
The rules are simple and maybe even a bit vague in places. However, some very basic policy rules such as frequently changing passwords and locking doors to server rooms should currently be a part of your basic office culture and those rules must also be stringently enforced by management.
Do you have a compliance officer? Why not? Do you have a HIPAA Disaster Recovery Plan and Compliance Manual? Do you know where it is? Why Not? Do you have a BAA contract for anyone touching your PHI? Are you SURE? Why not? Don’t even know what a BAA is? UH-OH…
These are a few of the breach creating, disaster in the making, nuclear bomb security holes that can easily be uncovered by an audit, then fixed. By putting enforced policies in place, you help insulate your practice from the wrath of big brother, and possibly more important, helps keep you from violating the promise you made to your patients, “we will protect your privacy”.
Pay attention to the writing on the “Wall of Shame”… the HIPAA Police are coming and they want to get paid.
Don’t give them a reason.
With 25+ years working in the technology sector with a combination of educational and technical support consulting, Doug is committed to delivering the right solutions and services for clients and business partners. dvanderbilt@network1consulting.com or 404.997.7644
Network 1 Consulting is a 17-year-old, IT Support company in Atlanta, GA. We become – or augment – the IT department for law firms and medical practices. Our IT experts can fix computers – but what our clients really value are the industry-specific best practices we bring to their firms. This is especially important with technology, along with regulations and cyber threats, changing so rapidly. We take a proactive approach to helping our clients use technology to gain and keep their competitive advantage.
Keep up with our latest tips at: