What is phishing?
 It is becoming a more frequent term in everyday life. The term is defined as an attempt to obtain sensitive information like usernames, passwords, and credit card information by disguising as a trustworthy entity in electronic communication. In other words, these bad boys and girls are going to send you fake emails all day long because they want your money or your information.
It is becoming a more frequent term in everyday life. The term is defined as an attempt to obtain sensitive information like usernames, passwords, and credit card information by disguising as a trustworthy entity in electronic communication. In other words, these bad boys and girls are going to send you fake emails all day long because they want your money or your information.
The act of a malicious sender disguising himself or herself as a trustworthy source is called Social Engineering. They have made some serious strides in the last decade. Though some phishing emails are easy to spot, many are dressed up very well. Sometimes these emails seem perfectly legit. They can come from a hacked email of a person you know with a Dropbox link they request you click. Or they come from a company you buy model trains from requesting that you reset your password. In both cases, if you do not spot them and you click these links, the bad guys now have your information.
Here are 3 key things you need to know to combat these attacks:
- Pay attention to the language.
- Check to see if the sender’s email address is the same as the company they say they are emailing you from.
- Use the cursor hover feature to check links before clicking.
Paying attention to the language
Language in the email can be a telltale for phishing attempts. These bad guys tend to use generic salutations such as “dear hiring manager” or “to whom it may concern.” They will also very politely try and get you to click on their filthy password-stealing links with language like “kindly click the link below” or “please open and verify the PDF.” Lastly, look for strange grammatical or spelling errors.
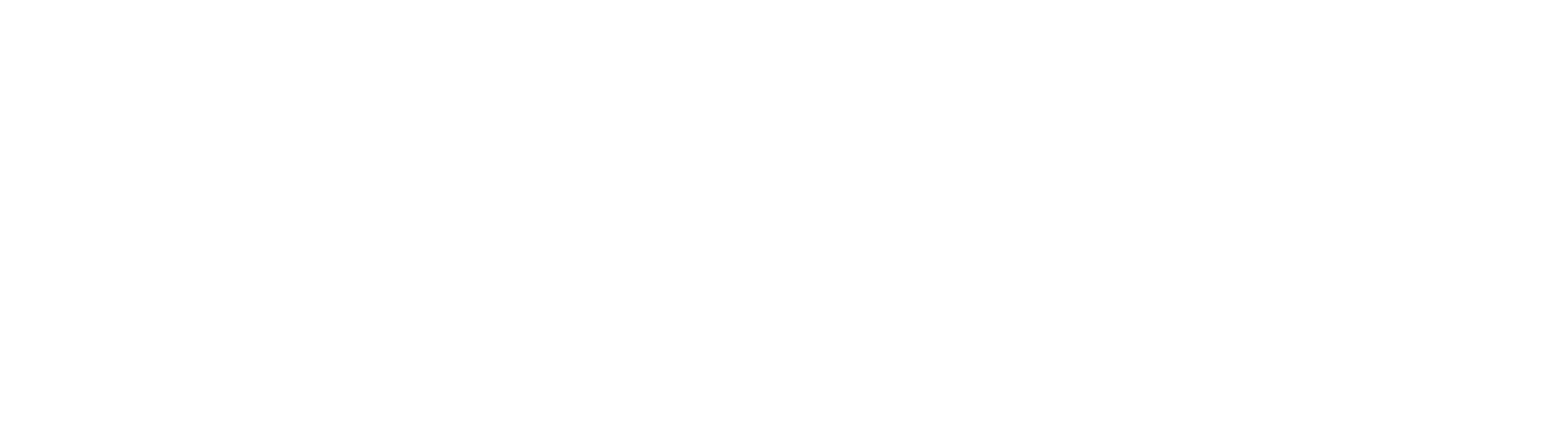
Checking the sender’s email
This is as straightforward as it sounds. You can see the sender’s email address of every email you receive. If you are ever asked to click a link or open an attachment by someone you do not normally do business with, make sure their email matches the company they say they represent. For example, let’s say you receive an email from “PayPal” stating that someone has tried hacking your account and you need to reset your password. The email looks legit. There are no errors, and it even has the company logo. But a quick look up at the sender’s email address and you can see the email did NOT come from johndoe@paypal.com but instead came from johndoe@imgoingtostealyourstuff.com. Now you know that email did not come from PayPal, and you can disregard it.
Cursor hover feature
The icon hover feature is extremely useful when trying to decipher whether an email is fake. HTML allows anyone to make a link say whatever they want. This is why you see blue “Click Here” buttons on websites or newsletters. Unfortunately, the bad guys take advantage of this and make links look like they are from legitimate companies. Going with our PayPal example, the sender might have sent you a link that looks like www.paypal.com/resetpassword. But if you hover your cursor over the link, the actual address the link points to will be revealed. In my experience, they actually look something like www.uhygerf@###256hudrgu!2.com once you hover over them.
Use these three methods when you feel suspicious of any email. Slowing down and doing some quick checks can save you money and a headache. Stay off the hook out there!
 Tony Coughlin
Tony Coughlin
With multiple years of experience in customer service across many industries, Tony brings his upbeat and positive attitude to the Network 1 team. He is committed to delivering the right solutions and services for clients and business partners.
tcoughlin@network1consulting.com or 404.997.7655
Network 1 Consulting is an 19-year-old, IT Support company in Atlanta, GA. We become – or augment – the IT department for law firms and medical practices. Our IT experts can fix computers – but what our clients value most are the industry-specific best practices we bring to their firms. This is especially important with technology, along with regulations and cyber threats, changing so rapidly. We take a proactive approach to helping our clients use technology to gain and keep their competitive advantage.