by Tony Rushin
In the land of computers, the bad guys are always lurking, plotting, and scheming. Over the last 12 months they seem to be more active than ever. Unfortunately, some of them are also very smart, which means their deception can trick even a savvy computer user.
Here are three recent real-life examples from our clients. We’ve already spread the word with the rest of our clients, via periodic “Alerts” that we send out, and wanted to share them more broadly. Feel free to pass any of our tips along to others – this one in particular because anything we can do to keep each other from falling prey to the bad guys is a good thing.
Example #1: Spoofing
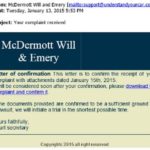
A law firm client received this email earlier this year:
It appears to be from a national law firm: McDermott, Will & Emery. However, a closer look reveals that the email address is from support@understandyourcar.com. Common variations of spoofing emails appear to be from Fedex, UPS, or Amazon.com. Be alert! Examine your emails carefully, especially if it’s from someone you don’t know. Never reply to an email, or click on an attachment or link, if you’re not sure. Hit “Delete”. If it turns out that it was legitimate, the real sender will find another way to contact you.
Example #2: Several Clues
As in the example above, malicious emails can be misleading and often look legitimate. After one of our clients received the following email, Michael Saba, a Network 1 engineer, pointed out some clues to help people determine what is safe (or unsafe) to open.
The clues:
- Do you know Frank Carruba?
- If not, it’s a clear indicator: NEVER click a “Dropbox” link from someone you do not know.
- If you do know Frank, were you expecting a document from him? If not, NEVER click an impersonal email asking to click on a “Dropbox” link when you were not expecting it. If there is any doubt, email the person you know (in a separate email; NOT by replying to the suspicious email) or call the sender and ask him to confirm.
- The language is very suspicious
- The subject “top urgent” is suspicious
- One does not attach a document “to” someone
- The lower case “i” is suspicious
- There is no information in the email indicating that they are sending something specifically intended for you. This email could, and probably did, go out to a million different people.
- © 2014 Dropbox
- Most importantly, the link redirects you to a site that is NOT Dropbox
- If you mouse over the link (but DO NOT click) you will see the contents of the hyperlink.
- If there is any doubt, you can also right click and “copy hyperlink”; then you can paste it into Notepad or a Word document (anything other than a browser).
- Here are the contents of that link: vertex-engineers.
Example #3: Phone Scam
Several of our clients have been the recipient of a phone call that goes something like this: “Hello, this is Joe from Microsoft (or Citrix, HP, Dell) calling to follow-up on the problems you’ve been experiencing. I’ll be sending you an email that contains a Dropbox link; just click on the link so I can access your environment and troubleshoot the problem.”
Please know that your IT support company/person doesn’t use Dropbox for technical support (and if they do, perhaps it’s time to look for another IT support company) and your software or hardware providers never use Dropbox for technical support. Network 1 would never have a hardware or software vendor contact any of our clients directly without giving the client a heads-up first (and your IT support company/person probably has a similar policy). You should report any such activity to your IT support company/person and feel free to provide the caller with your IT support company/person’s contact information.
Here are a few other previous Tuesday Tips and Alerts that we’ve sent to warn people about the things bad guys do to trick us:
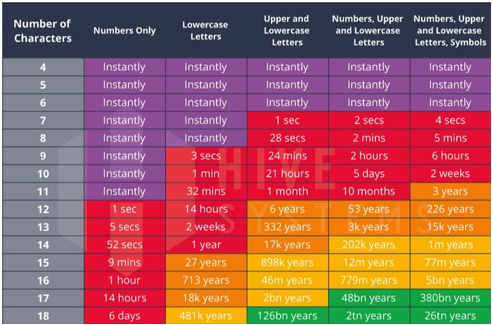
Tuesday Tip: Passwords and USBs – Beware!
Malware Alert: New Cryptolocker
Tuesday Tip: Protect Yourself from Phishing
Tuesday Tip: Be Careful Where You Re-Charge Your iPhone
Tuesday Tip: “Don’t Click That” and Other Wise Practices
Keep up with our latest tips at: