 Operating under a “bring your own device” (BYOD) policy has become more common for data-driven businesses in recent years. Employees appreciate the option to use preferred platforms and devices; employers typically reap cost savings in both hardware and training. The arrangement can work well for all involved, but it does pose additional risk from a data security standpoint.
Operating under a “bring your own device” (BYOD) policy has become more common for data-driven businesses in recent years. Employees appreciate the option to use preferred platforms and devices; employers typically reap cost savings in both hardware and training. The arrangement can work well for all involved, but it does pose additional risk from a data security standpoint.
Threats can come in the form of increased vulnerability to hacking attempts and theft of the devices themselves, or more subtle dangers like accidental disclosure of confidential information or even employee misuse of the data. While some extra risk is part and parcel of a BYOD approach, there are things employers can do to minimize the likelihood of serious problems stemming from the policy.
One critical step is to create and enforce a clear policy regarding acceptable use for the devices, if company-owned, and the data they contain. This policy should clearly communicate guidelines for choices regarding software, networks, platforms and devices, as well as ensuring employees understand the consequences of failure to abide by the stated rules.
Employers should also be certain to remind all users that confidential information needs to be carefully protected on every device, and that company data is company owned no matter where it may be stored or used.
Beyond drafting a formal policy to guide usage, businesses can consider a variety of actions that may reduce the risk of problems:
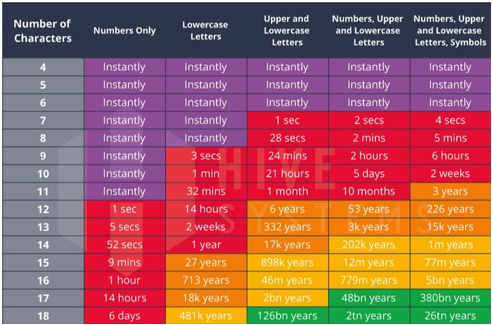
- Encrypt all data so that even if the device is hacked or stolen, the data it contains will remain secure.
- Institute a program to install and maintain up to date anti-virus and malware protection on all the devices that employees use.
- Arrange remote wipe and remote management of mobile devices so that the company has the ability to remove data and account access should a device be stolen or misused.
- Ensure that no data is stored on the devices themselves by providing remote access to servers.
- Implement a “walled garden” approach with apps that segregate personal and company data.
- Track data migration if it leaves company-controlled storage and usage areas.
Some of these tactics are more complicated than others, and not all businesses will want or need to employ all of them. Some, however, will want to explore all these strategies as well as other to protect sensitive, proprietary or confidential client information for which the company is responsible.
Being pro-active is always easier than dealing with data mishaps after the fact! If you need help figuring out the best ways to keep your data safe in a BYOD office environment, Network 1 is here to help.